If you haven’t done so already, it’s time to make sure you’re as prepared as you can for disruptions to digital platforms because of cyberattacks resulting from events unfolding in Ukraine.
To a large degree, there’s only so much you can do and while the risk to arts and culture organizations being targeted deliberately is low, the systems and platforms they rely on are much higher priority targets. At the most basic level, groups would be wise to consider the following:
- Confirm critical data is backed up.
- Reset account passwords for email, websites, social media platforms, and other digital providers that are 12 characters or longer. Use upper and lowercase letters, numbers, and special characters. Update them monthly until tensions subside.
- Ask your web developer and/or hosting provider to block all incoming traffic from countries other than those responsible for the lion’s share of legitimate traffic. Most reputable providers can put “block only” or “allow only from” rules in place.
- Use two factor authentication or similar added security measure (biometric, Yubikey, etc.) where available.
- Keep a very close eye on your websites and email clients to make sure they are not compromised and being used to spread malware or misinformation.
- Review how employees can identify phishing attacks (they have become remarkably more sophisticated in the last six months).
- Make sure company owned mobile devices are running the latest version of its operating system.
- Confirm key employees have a communication strategy if email service is unavailable.
Case In Point
Here’s a real-world example for item #5 from that list. Since the invasion of Ukraine, there’s been a huge uptick in spam misinformation from malicious Russian sources submitting comments that use compromised computers from countries outside of Russia.
This tactic is used to circumvent country wide blocks you can put in place for all web traffic originating from Russia. Hackers circumvent the process by using computers compromised from EU, UK, or North American locations. In these instances, hackers use a compromised computer to submit spam messages. In these instances, they are less concerned about gaining access to information. The only thing of value is the ability to hide the source of misinformation.
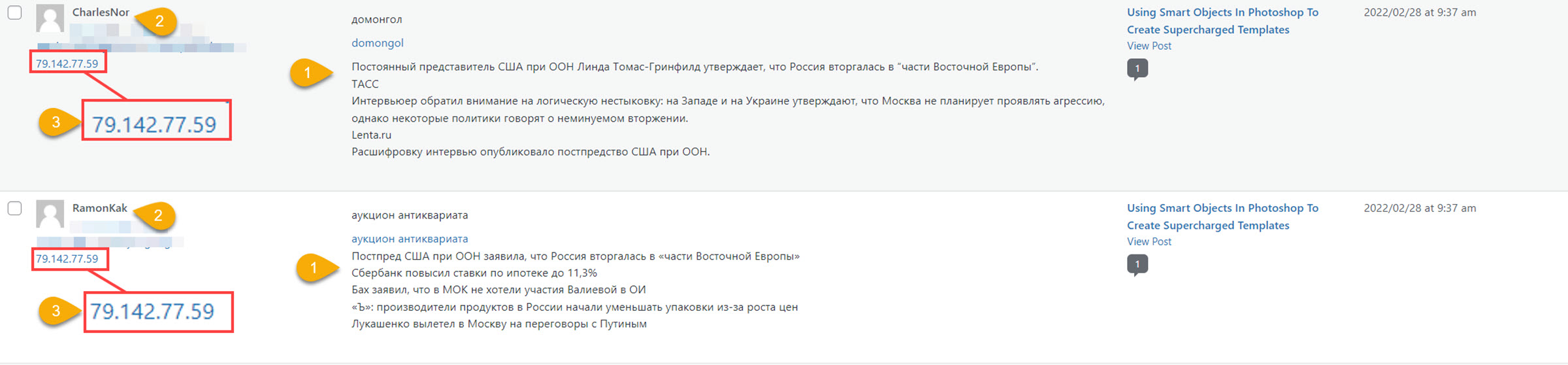
Here’s an example of two misinformation campaign messages that arrived here at ArtsHacker earlier today:
- The messages contain unique content. In this example, both are spreading misleading and false information. Repeating it here only serves their purpose, so I won’t bother.
- In an attempt to make the comments seem more legit, the username, email and website are unique between messages.
- This is the bit demonstrating that hackers are using compromised computers: this IP Address is in Stockholm, Sweden.
While most of this misinformation spam won’t see the light of day, that doesn’t matter to bad actors; for them, it’s all about quantity. It’s as simple as “throw enough mud against the wall…”
Don’t contribute to this unwittingly.
No doubt, it’s a pain in the ass to update passwords but doing so at your email clients, email marketing platforms, domain registrars, and websites will help cut down on this sort of malicious activity.
Thank you for the authoritative read on this issue. To me, being able to actually see the icon in the…